Safe Hospitality
Explore integrated technology designed to ensure safety and security in Upstate and Western New York restaurants, hotels, recreation and more from detection to final response
The Motorola Safety Reimagined Platform for Hospitality from Flower City Communications & Security
An All-Inclusive Approach To Safety And Collaboration
In the hospitality industry, exceeding guests’ expectations with exceptional customer service is job number one. Yet, in today’s world, customer experience begins with safety. We envision a world where technology works seamlessly together to combine intelligent awareness technology with fast, seamless communication to enable not only safety but also efficiency, from arrival to check out. We call this vision – Safety Reimagined.
The Motorola Solutions Safety Reimagined Platform unifies voice, video, data, and analytics technologies on one platform. With Safety Reimagined you can increase security, improve safety, reduce costs, boost efficiency, and improve communications across staff, teams, and locations. These solutions are designed with our customers’ needs at their core; helping Flower City Communications & Security deliver on our promise of creating a safer world.

Safety Reimagined – The Next Generation of Smart Technologies
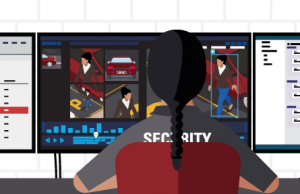
Improve Safety and Operations on One Platform
Leveraging Motorola’s Safety Reimagined Platform allows your day-to-day operations and emergency situations to be more manageable and measurable for predictable outcomes and optimizations.
Select a use case below and explore
The Safety Reimagined integrated technology ecosystem can provide meaningful outcomes for hotels, restaurants, recreation and more
Lost Child
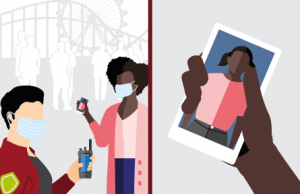
Lost child reported. A child is reported lost by their guardian to a nearby security officer or employee. An image of the child is provided and shared with appropriate staff.

Search initiated with video analytics. Using the provided image of the child, security teams can leverage the child’s appearance, shoes, or clothing, etc. as an identifying characteristic to begin an area search using video analytics.

Intelligence shared with field. Security teams are notified on where to begin the search. The image of the child is broadcasted to the entire security team and updates are continuously provided to relevant teams.

Situation resolved and documented. The lost child is located and returned to their guardian. An incident report is securely documented with all relevant information.
Secure area monitoring
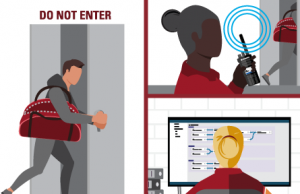
Access control breach recognized. Security teams receive an alert of a door breach in a secure area directly on the device of their choice and in the command center.

Situational awareness gathered. Relevant cameras are populated and the intruder is tracked throughout the facility and location of closest resources is determined.

Relevant personnel engaged. An image of the intruder is distributed to security teams and the path of the intruder is continuously updated to assist in interception.

Incident contained and reported. Security teams confront the intruder and escort them off the premises. An incident is logged with pre-populated fields and all relevant data.
Theft response
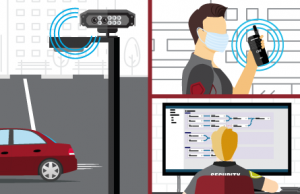
Unusual situation recognized. A vehicle is detected driving the wrong way in a parking lot. An alert is automatically sent to security directly on their device of choice and in the command center.

Suspicious activity observed. Security teams instantly populate all nearby cameras to evaluate the situation and observe individuals attempting to break into vehicles. Nearest security resources are located.

Security teams and public safety notified. Security teams are dispatched to the appropriate location and situational intelligence is continuously provided to relevant teams and local public safety is directly notified.

Situation contained and reported. Appropriate gates are closed off and the individual is detained. Video footage is delivered to local law enforcement. An incident report is filed and is shared with nearby sister-facilities.
Disruptive Guest

Disruptive guest reported. A staff member interacts with a disruptive guest and activates their body-worn camera. An alert is automatically sent to appropriate staff directly on their device of choice and in the command center.

Situational intelligence gathered. Security teams in the command center populate nearby cameras, including the body-worn camera and evaluate the situation to determine appropriate response.

Security staff engaged. Security teams are dispatched to the situation and receive intelligence including an image of the disruptive guest prior to their arrival on scene.

Situation contained and mitigated. Security confronts the individual to escort them off the premises. An incident report is securely documented with all relevant information and shared seamlessly with other nearby facilities.
Banned Individual

Individual recognized. The license plate of a known individual is recognized entering a parking lot. An alert is automatically sent to appropriate security staff directly on their device of choice and in the command center.
Known individual located. Nearby cameras are populated and security teams monitor the movement of the banned individual. Nearest security resources are located.

Security teams dispatched. Live video and intelligence is shared with security staff to intercept the individual and prevent hem from entering the facility. Public Safety is also directly alerted for assistance.

Situation contained and reported. The banned individual is prevented from entering the facility and real-time intelligence is shared with public safety. An incident report is securely logged with relevant information.
VIP Guest Experience

VIP guest recognized. A VIP guest or their associated license plate is identified and an alert is automatically sent to guest services and management to notify them of their arrival.

Situational awareness gathered. The operational command center receives the alert and all relevant camera feeds are populated. Guest services and management teams identify the individual and their current location.
Relevant personnel engaged.
Using two-way radios, guest services and management are dispatched to greet the guest at the appropriate entrance.

Optimal experience coordinated. Guest services and management welcome the guest and execute a heightened customer experience.
Learn How Safety Reimagined Can Help Your Operations
Safety Reimagined Voice, Video, Data, And Coordination Solutions from Flower City Communications & Security
Improve Safety And Security with a Coordinated Solution
Orchestrate workflow automation tool